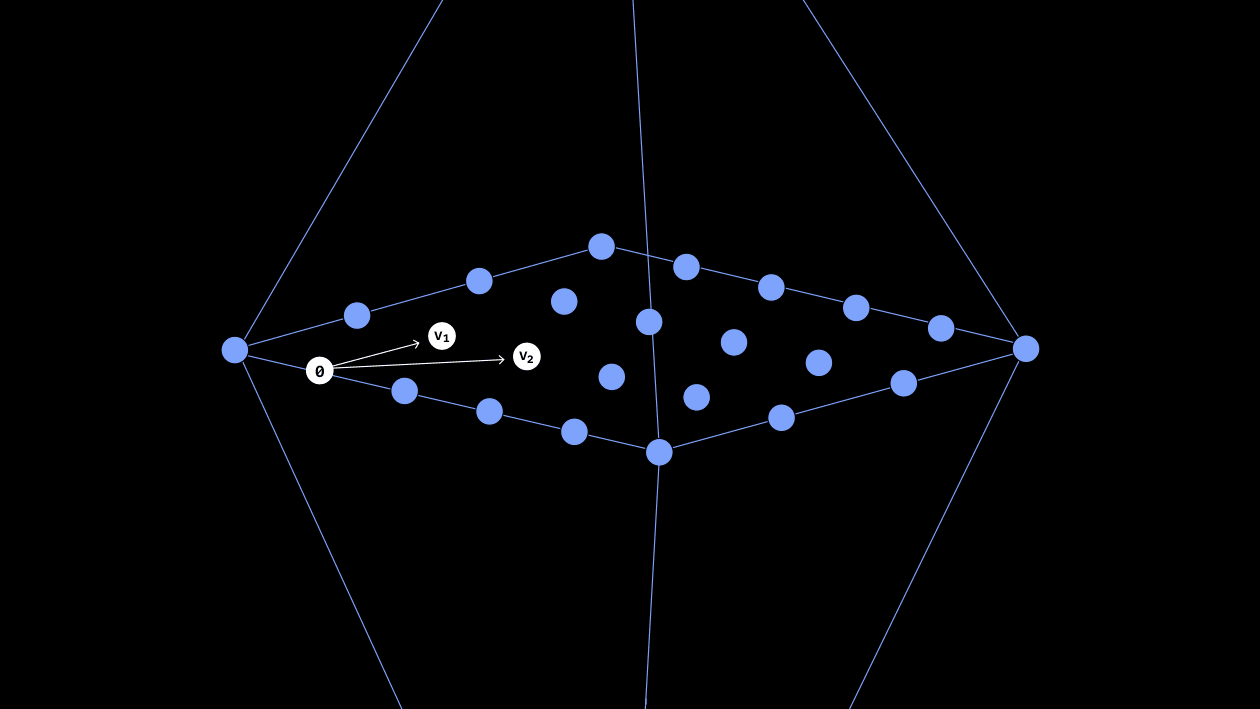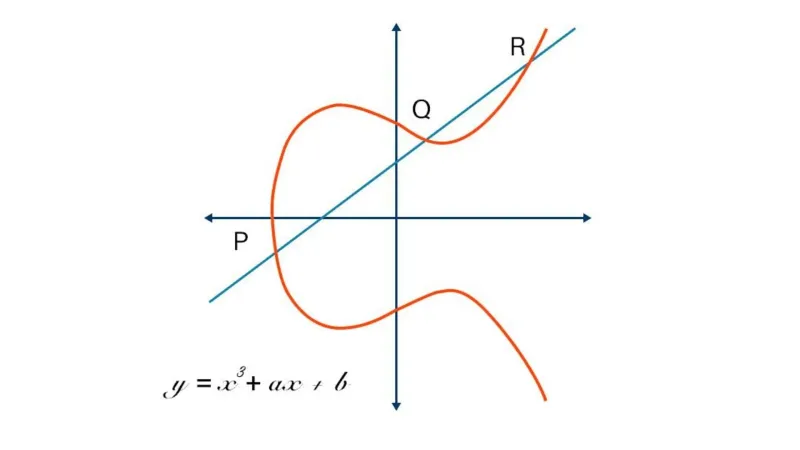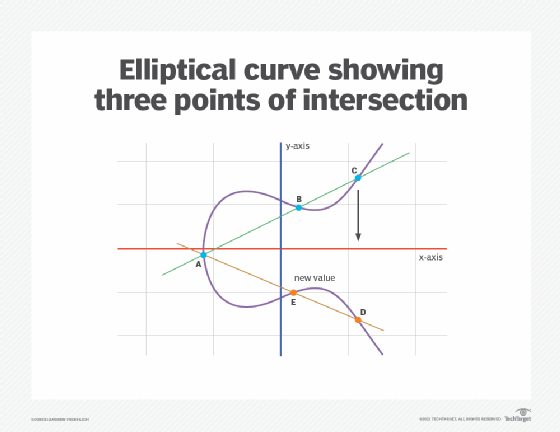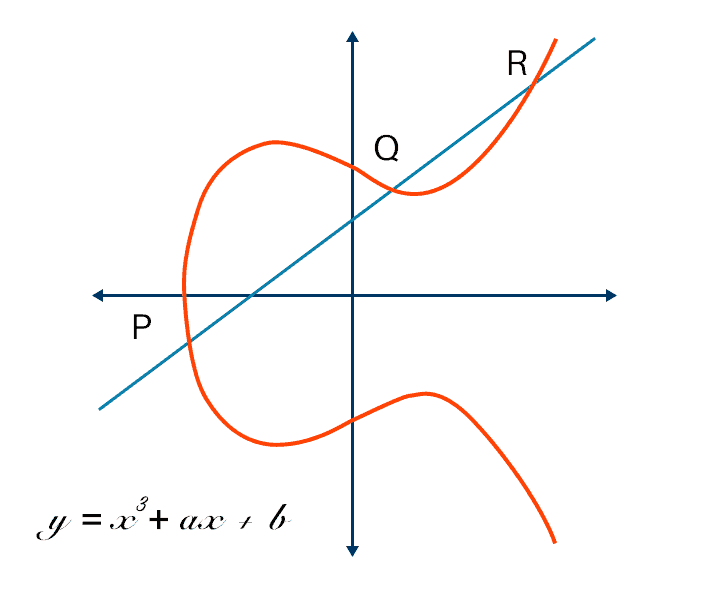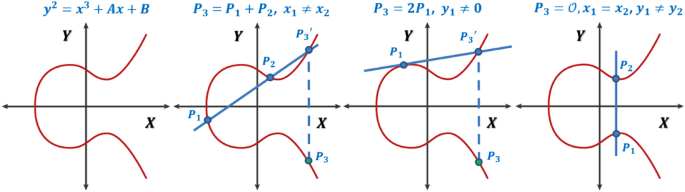
A generalized framework for elliptic curves based PRNG and its utilization in image encryption | Scientific Reports

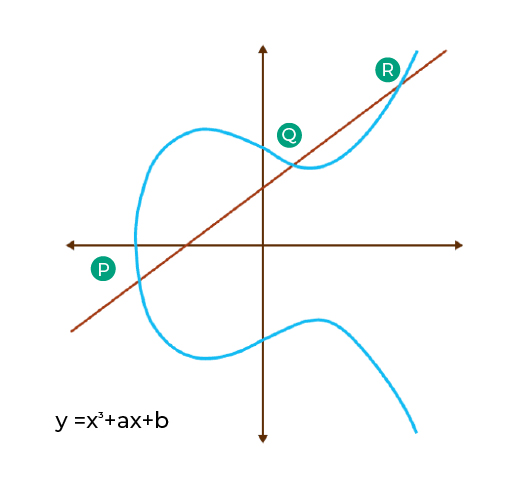
Everyone Loves Curves! But Which Elliptic Curve is the Most Popular? - Malware News - Malware Analysis, News and Indicators

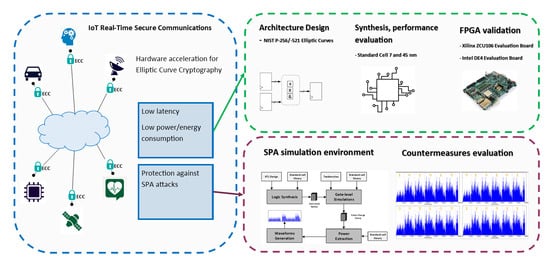
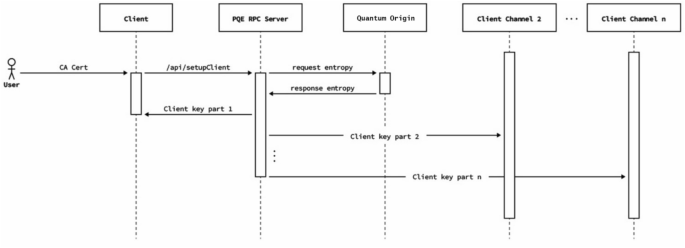
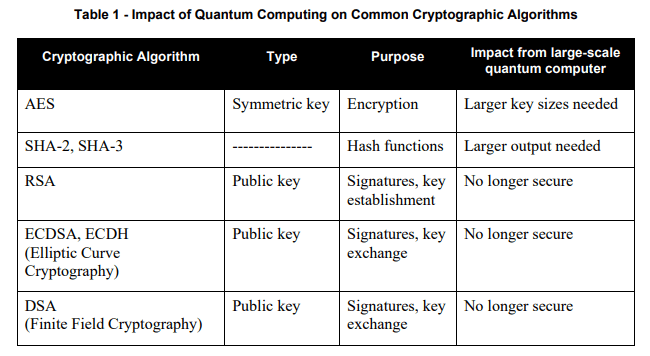
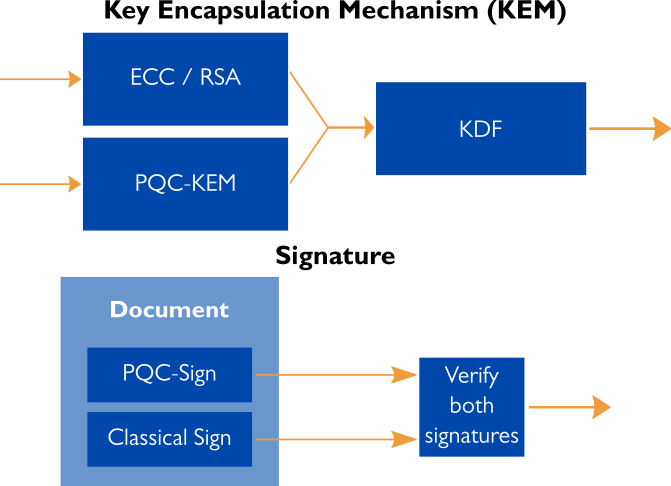
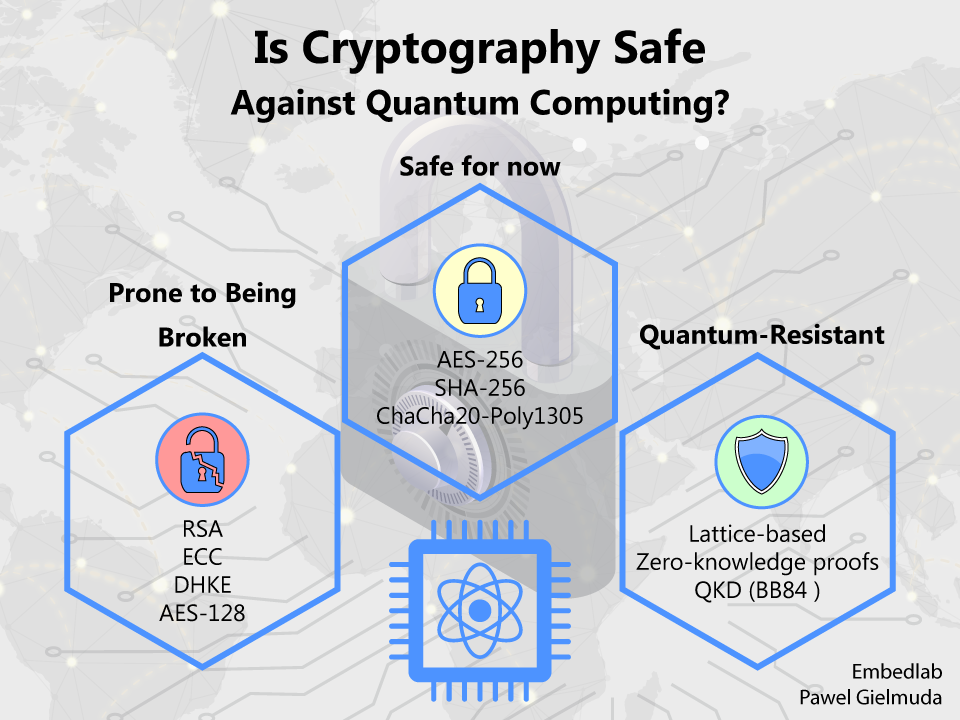
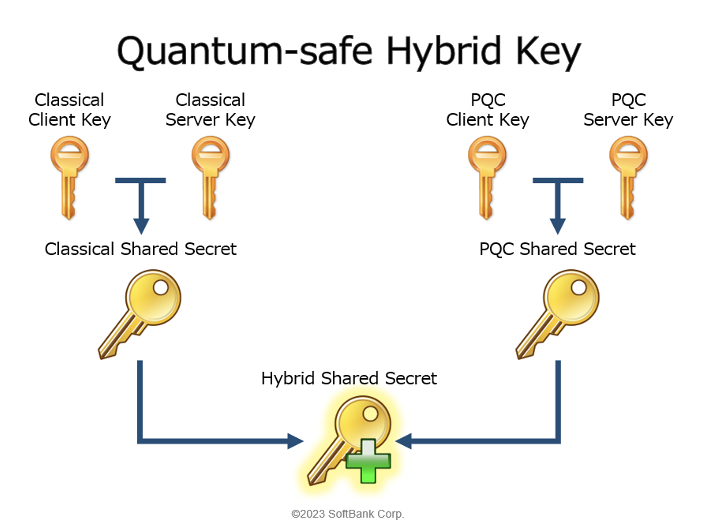
Sensors | Free Full-Text | Elliptic Curve Cryptography Considerations for Securing Automation and SCADA Systems